Mobile Malware – It’s Not Viruses You Should Worry About
While the world of mobile devices has grown to include everything from smartphones to tablets and wearables, your privacy is more and more at risk. Every day we hear about new attacks on one company or another. Edward Snowden revealed the mass surveillance the government is operating, and security researchers found that Verizon installs a “Permacookie” on your device to track your browsing habits. The outrage that was ensued evoked a world of security conscious consumers, or so you thought.
The media likes to hype up a story so that they have a “good story”, as such the web is crawling with warnings about mobile malware – malware targeted towards your smart devices. Researchers warn that the malware threat is growing daily, and it is, but it’s nothing to worry about. Last year Forbes published an article with some scary statistics: 97 % of mobile malware is on the Android platform. The article then goes on to explain that the malware comes from unregulated third party app stores, while at the time of writing a mere 0.1% actually came from the Play Store and those infected apps aren’t there for long. Android’s native security measures, coupled with Google’s rigorous scans of the apps on their market, make mobile devices much harder to target than your average PC.
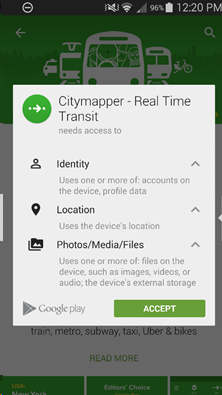
The real threat, however, doesn’t lie in virus infected repackaged apps or even the third party marketplaces. The real threat lies in the permissions of trusted applications, of those that do come from trusted sources. Any time you install an application your device greets you with an all too familiar screen.
The permissions screen isn’t expanded by default and many users pay no attention to the permission being requested. Worse yet, most developers don’t explain why they need these permissions, how they use them or what information they see and retain. The android platform makes certain permissions required for most application to function, however they are not elaborated on by Google or the developers and it leaves a wide range of information vulnerable to unsavory types. The example chosen here shows that a public transit app requires access to your photos, video or audio, yet offers no explanation as to why or, more specifically, which of these files are accessed.
Popular games are worse. Why would a game need access to my camera, photos or microphone? Do you really need to see my call logs because I want to play your game? What are these applications editing in device storage and why?
In most cases these permissions are simply to save game data, and reading your other data allows for targeted marketing, but where does the line get drawn? Do we really want advertising companies invading our privacy so they can target ads at us?
What of the other permissions? Why is it necessary to see my photos, or record voice data?
These answers may be very simple, and very benign, but without elaboration who knows what information they are seeing, or worse, selling?
Related
Related Posts
-
 CES 2019 Recap and Impressions!
No Comments | Jan 15, 2019
CES 2019 Recap and Impressions!
No Comments | Jan 15, 2019 -
WebOS Would Have Been 7 Yesterday
2 Comments | Jun 7, 2016 -
Samsung’s Attempt to Resurrect the Keyboard
No Comments | Aug 18, 2015 -
Earbud Cartilage Deficiency Disorder
No Comments | Apr 10, 2016
About The Author
CyberArcher
Carl is an Android enthusiast that got his start with an HTC Hero. Quickly tiring of not being able to change certain things about the device, he sought out the means to do what he wanted; Enter XDA Developers. After spending immense amounts of time on the forums learning, building and sharing, Carl decided to pursue higher education to increase his understanding and focus on a direction in the mobile world. Primarily focusing on security and privacy, Carl intends to gain his CEH and Reverse Engineer malware.



