Stagefright Still Takes Center Stage
 The Stagefright bug made quite a commotion among the mobile world when it was released. It’s rather scary to think that an embedded malicious code inside an MMS message, that doesn’t even need to be opened, can remotely control your device. This could be disastrous on personal devices, but exponentially so on enterprise devices. Beyond the ability to remotely crash a device, if cleverly crafted, this bug could create a botnet of Android devices. 950 Million of them. Though the likelihood of one hacker, or group of hackers, controlling 950 million devices is indeed infinitesimally small, the larger picture remains. Google, upon receipt of the bug and patches, immediately incorporated the patch into their code base and alerted manufacturers and carriers alike of the need for remediation.
The Stagefright bug made quite a commotion among the mobile world when it was released. It’s rather scary to think that an embedded malicious code inside an MMS message, that doesn’t even need to be opened, can remotely control your device. This could be disastrous on personal devices, but exponentially so on enterprise devices. Beyond the ability to remotely crash a device, if cleverly crafted, this bug could create a botnet of Android devices. 950 Million of them. Though the likelihood of one hacker, or group of hackers, controlling 950 million devices is indeed infinitesimally small, the larger picture remains. Google, upon receipt of the bug and patches, immediately incorporated the patch into their code base and alerted manufacturers and carriers alike of the need for remediation.
This is where the ball is dropped. Anyone who likes to play with Android knows that getting updates from the manufacturers or carriers is a struggle of epic proportions. This fact was highlighted by Google’s decision to slow their development from a 6-month release cycle to a 1-year release cycle back in 2014. This move allowed manufacturers a chance to keep up with current development, yet it still takes months after sources are made available to them before any updates are released, if they are at all. These months, coupled with the very short lifecycle of devices in the Android ecosystem, are what gives Stagefright its power. With an average lifespan of 6-months, a device that was new last Christmas may never see a patch for Stagefright. Businesses that leverage the Android platform for their mobile needs may be at risk because they just bought 400 tablets in May and they are EOL.
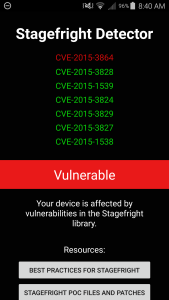
What’s more, Stagefright doesn’t appear to have been patched in its entirety. As illustrated by researchers at Exodus Intelligence, there are still vulnerabilities in the Stagefright library. I received an update for my device purporting to have patched Stagefright in the upgrade to 5.1.1 and decided to check it out after I learned of the possibility of still being vulnerable. I grabbed Zimperium’s Stagefright Detector app and let it run. As you can see in this post’s image, my “patched” device is still vulnerable to the CVE-2015-3864 vulnerability. While I applaud Google, Samsung and my carrier for their fast response and efforts to patch the bug, it still remains a valid security concern for me, not to mention those who have yet to receive any updates or patches, or never will.
Moral of this story kids, no matter what, software is still written by humans and as a friend of mine likes to say “If someone coded it, a someone else can break it”. There is a laundry-list of techniques that can be used to mitigate the damage or reduce the likelihood of Stagefright affecting your device:
- Disable Auto-Retrieval of MMS
- Restrict your messages to known contacts
- Be careful of sites visited on your mobile browser (Firefox has patched their browser against Stagefright)
- Use Google Hangouts rather than the stock Messaging app
These are a few of the most effective methods of combatting the possibility of an attack from this vector, but it’s far from being infallible. Until all patches are rolled out to all vulnerable devices, this bug may run a rampant rampage through the mobile ecosystem, unfettered by attempts to thwart the attack.




